In cloud environments, breach notification timelines become complicated because distributed architectures and shared responsibilities often delay detection and make pinpointing the breach origin harder. This can cause you to miss legal deadlines, especially across multiple jurisdictions with differing rules. Delays in forensic investigation and ambiguous responsibility further risk non-compliance. If you’re not prepared for these cloud-specific challenges, you could face serious legal and reputational consequences. Keep going to discover how you can better navigate these unexpected hurdles.
Key Takeaways
- Cloud environments obscure breach discovery timing due to distributed logs and encryption, complicating notification deadlines.
- Multi-jurisdictional breaches require navigating conflicting legal timelines, increasing compliance risks.
- Shared responsibility models can delay breach detection, risking missed reporting windows.
- Forensic investigations in the cloud often take longer, challenging timely breach notifications.
- Proactive detection and flexible response plans are essential to address unforeseen cloud-specific notification complications.

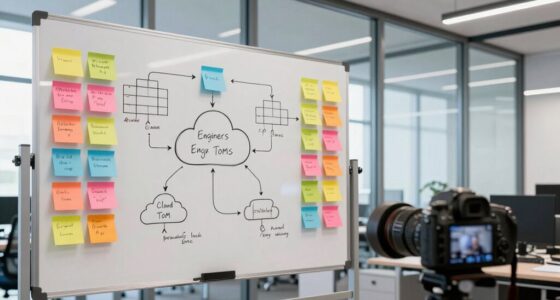
In today’s rapidly evolving regulatory landscape, breach notification timelines are becoming increasingly stringent and complex. You need to navigate a patchwork of state laws, federal rules, and international regulations, each with its own deadlines and exceptions. Many states have set firm 30-day deadlines for consumer notifications, like California’s SB 446, which takes effect in 2026, and others such as New York, Colorado, Florida, Maine, and Washington follow suit. Meanwhile, federal regulations like HIPAA require affected entities to notify individuals within 60 days of discovering a breach affecting more than 500 people. But these timelines often overlap and conflict, especially during cross-border incidents involving cloud-hosted data. When a breach impacts multiple jurisdictions, you must tailor notifications to each, considering different deadlines, content requirements, and regulator contacts, which complicates your response efforts. Legal requirements vary widely, making it essential to develop a comprehensive and flexible breach response plan. Law enforcement delays are common and permitted in many laws, allowing you to postpone notifications if disclosure might hinder an investigation. However, these delays often come with limits—some statutes restrict indefinite postponements, mandating fixed outer bounds. You might also be able to delay notification to determine the breach’s scope or restore system integrity, but these exceptions are narrower than they once were. When dealing with cloud environments, things get more complicated. Distributed architectures and multi-tenant models make it difficult to pinpoint exactly when the breach was discovered. Shared responsibility models blur the lines of accountability—who discovered the breach? You or your cloud provider? This ambiguity can delay your notification clock, risking non-compliance. Detection itself is harder in the cloud. Distributed logs, encrypted backups, and asynchronous data flows slow forensic investigations. It can take days or weeks to gather enough evidence, especially when involving third-party forensic teams or vendor cooperation. Without real-time telemetry or consistent log retention, your ability to quickly assess scope suffers, squeezing your window to notify affected individuals and regulators. These delays increase your legal and reputational risks and may lead to missed statutory deadlines. Adding to the challenge is the need to produce detailed, compliant notices supported by forensic evidence. Regulators expect clear explanations of how the breach occurred, what data was exposed, and what remedial actions you’re taking. Some jurisdictions even require submitting sample notices and communication copies, increasing your evidentiary burden. To stay prepared, your contracts should specify breach responsibilities, timelines, and forensic support obligations. Regular tabletop exercises involving legal, compliance, and cloud teams can help identify gaps, streamline your response, and ensure you meet these increasingly tight and complex notification deadlines. Recognizing the cloud-specific detection challenges early can help you implement proactive measures like real-time monitoring and automated alerts, which are crucial for timely breach identification in distributed environments.

SQL for Security Analysts: Detection Engineering, Forensics Queries, and Breach Response
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.
Frequently Asked Questions
How Do Organizations Coordinate Breach Notifications Across Multiple Jurisdictions?
You coordinate breach notifications across multiple jurisdictions by establishing a thorough legal and operational strategy. First, identify all applicable laws and deadlines. Then, create tailored communication plans for each region, ensuring translations and local requirements are met. Use centralized logs and automated tools for detection and documentation. Regularly train your team and vendors, run simulations, and keep clear records to guarantee timely, compliant disclosures everywhere your data resides.
What Legal Risks Arise From Delayed Breach Disclosures in Cloud Environments?
You risk legal penalties, fines, and reputational damage if you delay breach disclosures in cloud environments. Regulatory agencies expect prompt notifications; missing deadlines can lead to enforcement actions, civil liabilities, and breach of compliance standards. Delays also undermine trust, invite lawsuits, and may trigger audits. To mitigate these risks, guarantee clear contractual obligations, rapid forensic procedures, and coordinated response plans that align with evolving legal timelines and requirements.
How Can Companies Ensure Forensic Readiness in Ephemeral Cloud Systems?
To guarantee forensic readiness in ephemeral cloud systems, you should implement pre-approved snapshot workflows that capture system states immediately upon detection of a breach. Establish clear escalation paths with cloud vendors for rapid evidence collection and retention. Regularly test your forensic procedures, automate log aggregation, and document all steps taken. This proactive approach helps you meet legal timelines, preserve evidence integrity, and streamline investigations, minimizing delays and compliance risks.
What Contractual Clauses Best Address Cloud Provider Breach Notification Obligations?
You should include clear contractual clauses that specify breach notification obligations, timelines, and responsibilities of your cloud provider. Make certain they commit to notifying you promptly upon discovery of a breach, aligned with applicable laws. Also, require access to logs, cooperation during forensic investigations, and detailed escalation procedures. Incorporate SLAs for timely support, data preservation, and cooperation, so your company can meet statutory deadlines and minimize legal and operational risks.
How Do Safe-Harbor Provisions Impact Breach Disclosure Timelines?
You might find that safe-harbor provisions are a double-edged sword, as they can extend breach disclosure timelines or even temporarily halt notification obligations. These clauses often allow delays when investigations are ongoing or when law enforcement requests confidentiality. However, relying on them too heavily can backfire if regulators view delays as non-compliance. It’s essential to understand how these protections fit within jurisdictional laws to avoid missing statutory deadlines.

Mark Twain Forensic Investigations Workbook, Using Science to Solve High Crimes Middle School Books, Critical Thinking for Kids, DNA and Handwriting Analysis Labs, Classroom or Homeschool Curriculum
Students build unmatched deductive-reasoning skills as they become crime-solving stars
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.
Conclusion
Managing breach notification timelines in the cloud domain can be more intricate than it appears, often presenting unforeseen challenges. By staying vigilant and proactive, you can better manage these delicate situations and uphold your reputation. Remember, a well-prepared approach transforms potential complications into opportunities for trust and transparency. Embrace the complexity with confidence, knowing that your commitment to timely, responsible communication can turn a delicate circumstance into a testament to your professionalism.

HIPAA Package for Medical and Dental Offices Including Regulations and Standards Manual (hardcopy) + Policies and Forms (hardcopy and USB) + Training Outline and Test + Resource USB + Posters
A HIPAA compliance solution for healthcare providers like medical offices, dental offices and more
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.

BookFactory Security Pass Down Log Book/Security Guard Journal – Wire-O Logbook,100 Pages, 8.5'' x 11'' (Made in USA)
Made in USA – Proudly produced in Ohio by a Veteran-owned business
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.