Under NIS2, cloud teams often overlook critical responsibilities like clear role definitions for incident response, risk management, and compliance monitoring. Without assigning accountability for tasks such as vulnerability assessments, real-time incident detection, and reporting, gaps can form that threaten security and regulatory compliance. It’s crucial to establish who handles what to prevent overlaps or omissions. If you want to make certain your team’s responsibilities are fully covered, there’s more to consider to tighten your compliance efforts.
Key Takeaways
- Clear role delineation is often missing, leading to overlooked responsibilities in incident detection and response.
- Responsibility gaps frequently occur in vulnerability management and access control tasks within cloud operations.
- Many cloud teams lack formalized accountability for compliance monitoring and real-time security visibility.
- Undefined ownership for incident reporting and communication hampers timely notification to authorities.
- Without explicit responsibilities, teams risk non-compliance and increased vulnerabilities due to role ambiguity.

NETGEAR 26-Port PoE Gigabit Ethernet Smart Switch (GS724TP) - Managed, 24 x 1G, 24 x PoE+ @ 190W, 2 x 1G SFP, Optional Insight Cloud Management, Desktop or Rackmount
24 Gigabit Ethernet ports
As an affiliate, we earn on qualifying purchases.
Understanding NIS2: What Cloud Teams Need to Know

Understanding NIS2 is essential for cloud teams because it sets clear security requirements and responsibilities that impact your daily operations. The directive mandates technical and organizational measures to protect network and information systems, emphasizing a holistic approach to security. You need to understand whether your organization qualifies as an essential or important entity, as this influences your obligations, oversight, and potential penalties. NIS2 also requires risk management practices like vulnerability assessments, encryption, and continuous monitoring. Incident reporting is critical, with serious breaches needing to be reported within 24 hours. For cloud teams, this means maintaining real-time visibility, automating security processes, and ensuring your cloud environment complies with both national and EU regulations. Staying informed helps you proactively manage risks and avoid costly non-compliance penalties. Additionally, adopting a security-first mindset ensures that security is integrated into every aspect of your cloud operations. Recognizing the importance of compliance obligations can help prevent significant legal and financial consequences. Understanding the role of regulatory frameworks can further enhance your preparedness and response strategies. Being aware of security measures mandated by NIS2 enables your team to implement effective safeguards and respond swiftly to incidents. Incorporating cybersecurity best practices into your routine can significantly strengthen your overall security posture.

TP-Link 24 Port Gigabit Ethernet Switch Desktop/ Rackmount Plug & Play Shielded Ports Sturdy Metal Fanless Quiet Traffic Optimization Unmanaged (TL-SG1024S)
𝙊𝙣𝙚 𝙎𝙬𝙞𝙩𝙘𝙝 𝙈𝙖𝙙𝙚 𝙩𝙤 𝙀𝙭𝙥𝙖𝙣𝙙 𝙉𝙚𝙩𝙬𝙤𝙧𝙠: 24 port of 10/100/1000Mbps RJ45 Ports supporting Auto Negotiation and Auto MDI/MDIX
As an affiliate, we earn on qualifying purchases.
Clarifying Roles and Responsibilities in NIS2 Compliance

To guarantee compliance, you need to clearly define accountability lines across your team, so everyone understands their specific responsibilities. It’s also essential to identify where responsibility gaps may exist and address them proactively. Clarifying role expectations helps prevent overlaps and ensures effective incident response and risk management. Incorporating team collaboration strategies can further enhance coordination and accountability. Additionally, understanding the horsepower of electric dirt bikes can inform technical roles related to system performance and capacity planning. Recognizing role clarity is crucial for streamlining responsibilities and avoiding redundancies within your team. For example, understanding how floating on water techniques can improve team fluidity may offer unexpected insights into flexible responsibility sharing.
Defining Accountability Lines
Clear accountability is essential for effective NIS2 compliance, as it guarantees that each role understands its responsibilities and acts accordingly. You need to establish clear lines of authority and responsibility across your team, ensuring everyone knows their specific tasks in risk management, incident reporting, and security monitoring. Define who handles each aspect of compliance, from senior management setting policies to DevOps executing secure infrastructure changes. Use organizational charts and documented procedures to formalize these roles. Regularly communicate responsibilities through training and internal updates. Additionally, leveraging organizational structures can help clarify roles and streamline communication channels. By clarifying responsibility lines, you minimize overlaps and gaps, enabling swift decision-making and coordinated responses. Incorporating content organization best practices ensures roles are well-aligned and responsibilities are clearly delineated. Establishing responsibility matrices can further enhance clarity and accountability within your team. This structured approach helps your team stay compliant, reduces confusion, and ensures everyone contributes effectively to your NIS2 compliance efforts.
Sharing Responsibility Gaps
Sharing responsibility gaps often arise when roles and duties are not explicitly defined or communicated within your organization. Without clear boundaries, team members may assume others handle critical tasks like incident response, security assessments, or compliance checks. This can lead to role ambiguity, causing confusion about who is responsible for specific security functions. This confusion can lead to overlooked vulnerabilities, delayed incident detection, and non-compliance risks. For example, DevOps might assume security is someone else’s responsibility, while security teams believe DevOps manages infrastructure security. Such gaps create blind spots, increasing the chance of cyber threats slipping through. To prevent this, you need to establish transparent responsibilities and ensure everyone understands their specific duties related to NIS2 compliance. Clear communication and documentation are essential so that no critical aspect remains unaddressed, reducing overlaps and omissions that could compromise your security posture. Additionally, implementing well-defined roles can help clarify accountability and streamline your organization’s response to security challenges. Recognizing and addressing these responsibility gaps is crucial for maintaining a strong security framework. Incorporating specialized security tools tailored to your organizational structure can further mitigate these gaps by automating some responsibilities and providing clear audit trails, which enhance accountability and support ongoing compliance efforts.
Clarifying Role Expectations
Understanding and defining role expectations is essential to guarantee your team complies with NIS2 requirements effectively. Clear roles prevent overlaps, gaps, and confusion during security incidents and compliance checks. You must specify responsibilities for governance, risk management, incident reporting, and monitoring. Use organizational charts and documented policies to communicate these roles. Assign ownership for tasks like vulnerability management, access controls, and incident response. This clarity streamlines decision-making and enhances accountability. Recognizing the importance of role clarity helps organizations align their security efforts with regulatory expectations and operational needs. Additionally, establishing responsibility documentation helps maintain consistency and accountability over time. Incorporating clear communication channels ensures that team members understand their duties and can collaborate efficiently during critical situations. Emphasizing role definition ensures that everyone knows their specific duties, reducing ambiguity and improving overall security posture. Moreover, regular training and updates on security responsibilities foster a proactive security culture within the team.

TP-Link 24 Port Gigabit Switch Easy Smart Managed Plug & Play Desktop/Rackmount Sturdy Metal w/ Shielded Ports Support QoS, Vlan, IGMP & LAG (TL-SG1024DE),Black
24-Gigabit ports provide instant large file transfers
As an affiliate, we earn on qualifying purchases.
Integrating Risk Management Into Cloud Operations

To effectively manage risks in your cloud operations, you need to implement continuous risk assessments and leverage automated security monitoring tools. These practices help you detect vulnerabilities early and respond swiftly to threats. Adopting risk-aware deployment practices guarantees your cloud environment stays compliant and resilient against evolving cyber threats. Incorporating smart appliances and connected systems into your risk management approach can further enhance your ability to identify potential issues proactively. Additionally, understanding home energy integration concepts can provide insights into how connected systems may impact overall security and operational stability. Being aware of filtration systems used in connected devices can help prevent security breaches caused by compromised hardware components.
Continuous Risk Assessment
Integrating continuous risk evaluation into cloud operations guarantees that security measures adapt dynamically to changing threats and system configurations. You need to regularly analyze vulnerabilities, evaluate risks, and update mitigation strategies to stay ahead of emerging threats. This involves ongoing monitoring of cloud resources, assessing new deployments, and reviewing access controls to detect potential weaknesses. Automated tools can help you identify configuration drift, vulnerabilities, and unusual activity swiftly. By embedding risk assessments into daily operations, you ensure that security remains proactive rather than reactive. You’ll also prioritize resources based on current threat levels, making your defenses more effective. Continuous assessment keeps your cloud environment resilient, compliant, and prepared for evolving cyber risks, fulfilling your obligation under NIS2 to maintain robust security postures.
Automated Security Monitoring
Automated security monitoring is the backbone of effective risk management in cloud operations. It continuously scans your infrastructure for unwanted changes, suspicious activities, and vulnerabilities, providing real-time alerts to minimize response times. By deploying commercial and custom tools, you gain visibility across servers, storage, networks, and services, guaranteeing no threat goes unnoticed. Infrastructure as Code (IaC) governance automates provisioning, enforcing secure configurations, while drift detection ensures your cloud environment stays aligned with your code and compliance standards. Automated monitoring supports incident detection, enabling swift reporting and response. It also underpins business continuity through proactive identification of risks before they escalate. By integrating these automated processes, you reduce manual oversight, improve resilience, and stay aligned with NIS2 requirements, ensuring your cloud operations are resilient, compliant, and secure.
Risk-aware Deployment Practices
Effective cloud deployment requires embedding risk management directly into your operational practices, ensuring security isn’t an afterthought. You need to proactively identify, assess, and address potential vulnerabilities throughout the deployment process. Consider these key practices:
- Conduct thorough risk assessments before deploying new resources, evaluating potential security impacts.
- Enforce strict access controls and least-privilege principles during deployment to minimize exposure.
- Automate security checks and compliance scans to catch misconfigurations early.
- Implement continuous monitoring to detect and respond to anomalies or unauthorized changes swiftly.
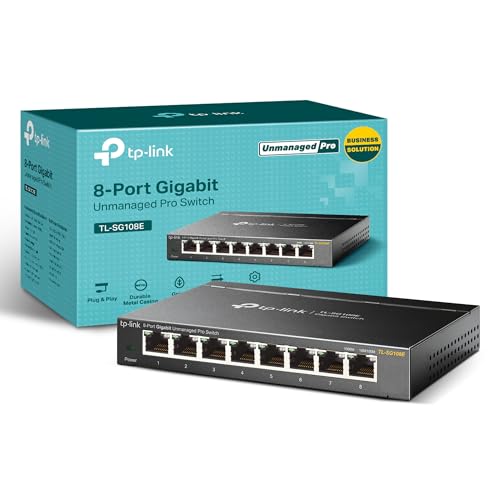
TP-Link 8 Port Gigabit Switch | Easy Smart Managed | Plug & Play | Desktop/Wall-Mount | Sturdy Metal w/ Shielded Ports | Support QoS, Vlan, IGMP and LAG (TL-SG108E)
𝟴 𝗚𝗶𝗴𝗮𝗯𝗶𝘁 𝗘𝘁𝗵𝗲𝗿𝗻𝗲𝘁 𝗣𝗼𝗿𝘁𝘀: expand your network with 8 high-speed ethernet ports
As an affiliate, we earn on qualifying purchases.
Incident Detection, Reporting, and Response Strategies

To guarantee swift and accurate incident management, it’s essential to have clear detection, reporting, and response strategies in place. You need protocols to identify incidents quickly, such as automated alerts from monitoring tools that flag suspicious activities or unauthorized changes. Reporting procedures should be straightforward—report serious incidents to authorities within 24 hours, following predefined steps. Your team must have well-documented runbooks and real-time visibility into cloud environments to enable rapid response. Regular testing of these procedures ensures everyone knows their role during an incident. Collaboration with national authorities and frameworks like EU-CyCLONe enhances coordination during large-scale events. Ultimately, proactive detection, quick reporting, and structured response plans minimize impact and strengthen your overall security resilience.
Monitoring Cloud Resources for Security and Resilience

Monitoring cloud resources is essential for maintaining security and ensuring resilience against disruptions. You need to keep a close eye on infrastructure, servers, storage, and network activity to detect issues early. Using both commercial and custom tools helps you identify unwanted changes and suspicious behaviors quickly. Regular monitoring minimizes reaction times and prevents minor issues from escalating. To effectively monitor, focus on these key areas:
Effective cloud monitoring detects issues early, prevents escalation, and ensures security across infrastructure, servers, storage, and networks.
- Track infrastructure and service health continuously to spot anomalies.
- Detect unauthorized or unexpected modifications through automated alerts.
- Monitor network traffic for suspicious or malicious activities.
- Guarantee Infrastructure as Code (IaC) configurations stay compliant with governance standards.
Preparing Your Organization for Regulatory Audits

Preparing your organization for regulatory audits begins with establishing thorough documentation that demonstrates compliance with standards like NIS2, ISO 27001, and PCI-DSS. You need clear evidence of policies, procedures, and controls in place. Maintain an up-to-date inventory of cloud resources, configurations, and security assessments. Regularly conduct internal audits and risk assessments to identify gaps. Ensure training records, incident reports, and remediation actions are well-documented. Use the following table to organize your audit readiness:
| Documentation Type | Purpose | Frequency |
|---|---|---|
| Security Policies | Define controls | Annually |
| Audit Reports | Evidence compliance | Quarterly |
| Incident Logs | Track incident management | Ongoing |
This systematic approach helps streamline audits and demonstrates your compliance efforts effectively.
Addressing the Gaps: Who Handles What in NIS2 Implementation

Implementing NIS2 effectively requires clear role delineation across your organization, guaranteeing each team understands its specific responsibilities. Without this clarity, gaps can appear, risking non-compliance and security breaches. To address this, define who handles what:
- Governance and Compliance Teams: Establish policies, oversee risk management, and ensure adherence to standards like ISO 27001 and PCI-DSS.
- Cloud Operations and DevOps: Manage infrastructure, monitor resources, implement automated security controls, and detect deviations through IaC governance.
- Incident Response Teams: Handle incident detection, reporting, and coordination with national authorities within the required timeframes.
- Senior Management: Set responsibilities, allocate resources, and ensure ongoing compliance and training across teams.
Clear responsibilities streamline NIS2 implementation and improve your organization’s resilience.
Frequently Asked Questions
How Does NIS2 Impact Third-Party Cloud Service Providers?
NIS2 requires third-party cloud service providers to meet strict security and compliance standards, guaranteeing they implement appropriate technical and organizational measures. You must oversee supply chain security, enforce risk management, and promptly report significant incidents. It’s your responsibility to maintain transparency, conduct regular security assessments, and ensure your services align with EU regulations. This means active monitoring, clear communication, and continuous improvement to protect client data and uphold resilience.
What Are the Penalties for Non-Compliance Specific to Cloud Teams?
You know what they say, “better safe than sorry.” For cloud teams, non-compliance with NIS2 can lead to hefty fines of up to 10% of your annual turnover or managerial bans. You’re responsible for ensuring security measures, incident reporting, and risk management are in place. Fail to do so, and you risk financial penalties, reputation damage, or even operational bans—so stay vigilant and proactive to avoid these serious consequences.
How Should Cloud Teams Handle Cross-Border Incident Reporting?
You should establish clear procedures for cross-border incident reporting, ensuring rapid communication with relevant national authorities and EU bodies like EU-CyCLONe. Keep detailed records of incidents, assess their impact, and report significant events within 24 hours as required. Collaborate with international partners, use automated tools for real-time detection, and regularly review your protocols. Staying proactive helps you comply swiftly and effectively, minimizing disruptions and penalties.
What Tools Are Recommended for Continuous Compliance Monitoring?
You should use automated tools like vulnerability scanners and compliance management platforms to guarantee continuous monitoring. These tools provide real-time insights, quick detection of deviations, and automated reporting, giving you proactive control. Pair them with Infrastructure as Code (IaC) governance and drift detection to maintain consistent configurations. While manual audits are essential, automation accelerates compliance, reduces errors, and helps you stay ahead of evolving threats and regulatory demands seamlessly.
How Can Cloud Teams Demonstrate Compliance During Audits?
To demonstrate compliance during audits, you should maintain detailed documentation of your security policies, procedures, and controls. Regularly conduct internal audits and vulnerability assessments, and keep records of findings and remediation efforts. Utilize automated tools to generate reports on security posture, access controls, and incident response. Additionally, guarantee your team is trained on compliance requirements and can provide evidence of ongoing monitoring, testing, and improvements, showing proactive management of security obligations.
Conclusion
Just as a captain must know every corner of their ship, you need clear roles under NIS2 to steer your cloud operations safely. Without assigning responsibilities, you risk steering stormy waters blindfolded. By clarifying who handles what, you ensure your organization stays resilient—like a lighthouse guiding ships through fog. Embrace your role confidently, and let NIS2 be the steady hand that keeps your cloud secure and compliant.









