To find single points of failure quickly through dependency mapping, you should visualize your system’s components and their relationships. Focus on identifying essential servers, switches, or services whose failure could cause widespread issues. Use automated tools and clear diagrams to spot these vulnerabilities promptly. Regularly updating your dependency maps helps you stay aware of potential risks as the system evolves. Keep exploring to learn how to strengthen your system’s resilience effectively.
Key Takeaways
- Use visual dependency maps to quickly identify components whose failure impacts multiple systems, revealing SPOFs.
- Leverage automated tools to continuously monitor and update dependency diagrams for real-time failure detection.
- Focus on critical nodes such as central servers and network switches that serve as potential SPOFs.
- Analyze both hardware and software dependencies to uncover hidden chains that could cause cascading failures.
- Prioritize risk mitigation by addressing dependencies with the highest impact on system resilience and availability.

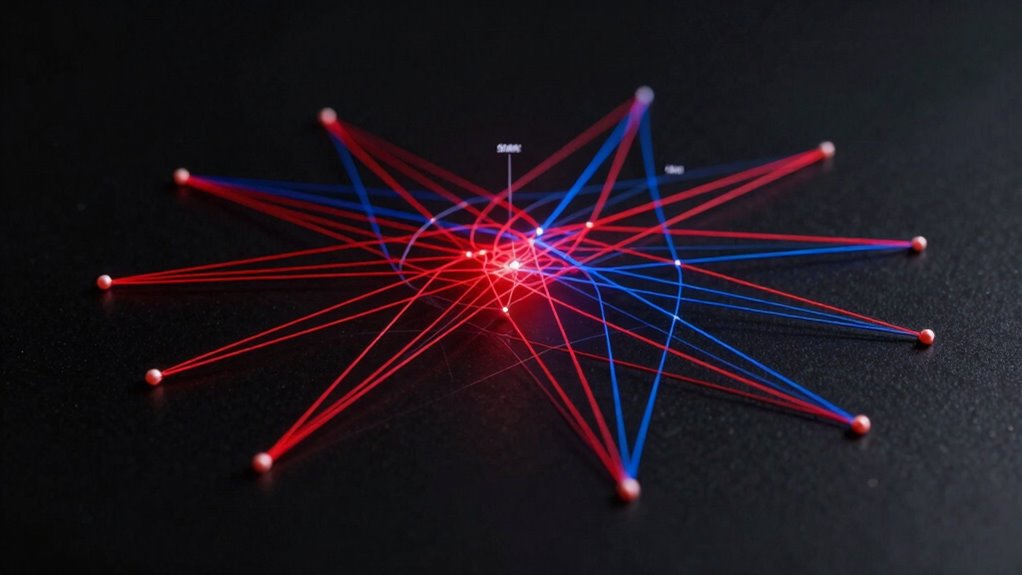
Have you ever wondered how interconnected components within your system can create hidden vulnerabilities? Dependency mapping offers a clear answer by helping you visualize and understand how your system’s elements interact. It involves creating visual representations like maps, flowcharts, or diagrams that show the relationships between software modules, infrastructure, and tasks. This process is vital for identifying single points of failure (SPOFs), which are components whose failure can cause cascading disruptions across your entire system. Whether it’s a vital server, a network switch, or a human dependency, recognizing these vulnerabilities early helps you prevent costly outages and data loss.
Dependency mapping visualizes system interactions to identify critical vulnerabilities and prevent cascading failures.
To perform dependency mapping effectively, you start by identifying all key components, including hardware, software, and human elements involved in your system. Next, analyze how these elements relate and depend on each other. For software, this means examining libraries, modules, and external services—both direct dependencies, which are explicitly declared, and transitive dependencies, which are indirectly included. For infrastructure, you’ll look at how servers, virtual machines, and networks connect and support each other. You can gather this data from version control systems, package managers, runtime monitoring tools, and system logs. Once collected, you create diagrams that clearly illustrate these relationships, making it easier to spot critical dependencies and potential SPOFs. Understanding these dependencies also involves recognizing how dependency relationships can influence system stability and resilience.
Visualizing dependencies isn’t just about creating pretty charts; it’s a strategic move to identify vulnerabilities that could threaten your system’s stability. For example, a single router handling all network traffic or a centralized database without backups can become a SPOF, risking widespread service outages. By mapping these dependencies, you reveal hidden chains and understand how a failure in one component can cascade through your system. This insight allows you to prioritize risk management efforts, develop contingency plans, and implement redundancies where needed.
Dependency mapping also improves your ability to manage technical debt and plan future upgrades. It clarifies how changes in one part of your system might ripple outward, enabling you to make informed decisions. Automated tools and specialized software can speed up this process, providing topology maps and real-time dependency discovery. Regularly updating your maps ensures you stay aware of evolving vulnerabilities as your environment changes. With a detailed dependency map, you gain the power to act swiftly when issues arise, reducing downtime and enhancing security.
Ultimately, dependency mapping isn’t just about understanding your system—it’s about proactively safeguarding it. By identifying SPOFs early, you can design redundancy strategies, improve resilience, and keep your services running smoothly. The clearer your visualization, the quicker you can respond to failures, minimizing risks and maintaining trust with your users. It’s an essential practice for anyone managing complex systems, helping you find critical vulnerabilities fast and stay ahead of potential disruptions. Understanding system dependencies is fundamental to maintaining a reliable and secure infrastructure.
network dependency mapping tool
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.
Frequently Asked Questions
How Often Should Dependency Maps Be Updated?
You should update your dependency maps at least annually or whenever significant changes occur in your systems, processes, or infrastructure. Regular updates guarantee you identify new SPOFs and vulnerabilities promptly. Keep an eye on technology upgrades, new integrations, or organizational shifts that could introduce risks. Frequent reviews help you maintain an accurate, current picture of dependencies, enabling you to act quickly and prevent cascading failures.
What Tools Are Best for Dependency Mapping?
Think of dependency mapping tools as your compass in a storm. You’ll want to use options like Microsoft Visio for detailed diagrams, Lucidchart for collaborative visuals, and SolarWinds Network Topology Mapper for real-time network insights. These tools help you visualize complex interactions, identify SPOFs quickly, and streamline risk assessment. Combining them guarantees you can spot vulnerabilities before they cause system failures, keeping your infrastructure resilient and reliable.
Can Dependency Mapping Prevent All SPOFS?
Dependency mapping can’t prevent all SPOFs, but it markedly reduces your risk. By visualizing interactions and dependencies, you identify weak spots that could cause cascading failures. Once you know these points, you can implement redundancy, backups, or alternative pathways. While it’s not foolproof, this proactive approach helps you spot vulnerabilities early, allowing you to address potential SPOFs before they cause system-wide disruptions.
How to Prioritize Fixing Identified SPOFS?
Prioritizing fixing SPOFs is like triaging a medical emergency—you focus on the most crucial threats first. You should assess each SPOF’s likelihood and potential impact, then rank them accordingly. Use risk heatmaps and severity ratings to guide your decisions. Address the highest risks with redundancy or failover solutions first, ensuring the most essential systems stay operational. Regularly review and adjust priorities as your environment evolves to minimize vulnerabilities effectively.
What Role Do Human Factors Play in Dependency Mapping?
You play a vital role in dependency mapping by identifying human factors that could become SPOFs. You need to recognize reliance on single individuals or teams for key processes, as their absence or error can cause cascading failures. By involving stakeholders and documenting workflows, you guarantee human dependencies are transparent. This helps you develop mitigation plans like cross-training, reducing risks and improving system resilience against human-related failures.

Software Failure: Management Failure: Amazing Stories and Cautionary Tales (Wiley Series in Software Engineering Practice)
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.
Conclusion
By quickly identifying single points of failure through effective dependency mapping, you can prevent costly downtime and keep your systems resilient. Did you know that 82% of IT outages are caused by human errors or overlooked dependencies? Staying proactive with dependency mapping not only reduces risks but also boosts your confidence in your infrastructure’s stability. Make this a priority, and you’ll stay ahead of potential failures before they impact your business.
hardware dependency diagram software
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.

Infrastructure Monitoring with Amazon CloudWatch: Effectively monitor your AWS infrastructure to optimize resource allocation, detect anomalies, and set automated actions
As an affiliate, we earn on qualifying purchases.
As an affiliate, we earn on qualifying purchases.