Identity federation enables seamless single sign-on across multiple domains without compromising security. It relies on protocols like SAML, OAuth2, and OpenID Connect to securely exchange authentication tokens, reducing password exposure and centralizing access controls. By trusting identity providers and enforcing strict validation, you can minimize vulnerabilities like token theft or misconfiguration. If you want to learn how to implement these robust practices and keep your federation secure, you’ll find practical strategies to explore further.
Key Takeaways
- Federation enables seamless SSO across multiple domains by trusting identity providers to authenticate users securely.
- Protocols like SAML, OAuth2, and OpenID Connect facilitate secure token exchange between IdPs and service providers.
- Proper token validation, short-lived tokens, and secure communication channels prevent security gaps in federation.
- Implementing strong MFA and strict attribute controls enhances security while maintaining user convenience.
- Regular monitoring, policy enforcement, and layered defenses mitigate vulnerabilities and protect federated identities.

Cudy New Gigabit Multi-WAN VPN Router, Up to 4 Gigabit WAN Ports, SMB, Load Balance, Lightning Protection, PPTP L2TP WireGuard OpenVPN IPsec VPN Router
Gigabit Multi WAN Router: 1 Gigabit WAN Port + 3 Gigabit WAN/LAN Ports +1 Gigabit LAN Port. Support...
As an affiliate, we earn on qualifying purchases.
Core Concepts and Architecture of Federation

Federated identity links user identities across different security domains, allowing authentication in one domain to grant access in another without requiring separate credentials. This setup relies on trust relationships established between identity providers (IdPs) and service providers (SPs). Standard protocols like SAML, OAuth2, and OpenID Connect facilitate secure exchange of assertions or tokens, which contain authentication results and user attributes. These tokens are validated by the IdP, reducing direct credential sharing with SPs. Federation architecture often follows models such as hub-and-spoke, brokered federation, or direct trust relationships. Each pattern balances control, scalability, and complexity. The core idea is enabling seamless, cross-domain Single Sign-On while maintaining security through trusted protocols and well-defined trust boundaries. Additionally, the use of high refresh rates in projectors can enhance the clarity and responsiveness of dynamic visuals, which is crucial for immersive experiences. Understanding the trust relationships within federation architectures is essential to ensure secure and effective identity management across diverse domains. Moreover, establishing clear security protocols is vital to prevent vulnerabilities and ensure the integrity of the federated identity system. Recognizing the importance of vetted standards like SAML and OAuth2 can help organizations implement more secure and reliable federation solutions. Furthermore, implementing standardized protocols promotes interoperability and reduces integration challenges among different systems.

ASUS ExpertWiFi EBG15 Gigabit VPN Wired Router, up to 3 WAN ethernet Ports + 1 USB WAN, IPS Intrusion Prevention, Layer 7 Firewall, Commercial-Grade Network Security, Remote Management with App
Easier-Than-Ever Setup — Convenient and easy router management via web browser or the ASUS ExpertWiFi mobile app through...
As an affiliate, we earn on qualifying purchases.
Security Benefits of Federated Identity Management

By centralizing authentication processes, federated identity management enhances security in multiple ways. You reduce the attack surface by lowering the number of passwords users need to remember, decreasing the risk of credential theft. Credentials are validated by the identity provider (IdP), so service providers (SPs) never see user passwords, minimizing exposure. Modern protocols like SAML, OAuth2, and OIDC ensure assertions are signed and validated, supporting integrity and replay protections. Additionally, federation enables strong multi-factor authentication (MFA) at the IdP, extending security to SPs without additional setup. Centralized logging improves detection and forensic analysis across federated sessions. Understanding authentication protocols helps clarify how these protections work together to secure user identities, especially when considering identity federation standards and best practices. Implementing secure communication channels further fortifies the overall security architecture, leveraging encryption techniques to safeguard data in transit.

SonicWall TZ570W Wireless Gen7 Firewall | PoE Multi-Gig Security Appliance with 3.0 Gbps Throughput, Integrated PoE, SD-WAN, and Full Threat Protection (02-SSC-2835)
SonicWall TZ570W Appliance Only - No Service Subscription (02-SSC-2835) - Delivers the multi-gigabit performance of the TZ570 while...
As an affiliate, we earn on qualifying purchases.
Recognizing Common Vulnerabilities and Threats

Understanding common vulnerabilities and threats in identity federation is essential because attackers often exploit weaknesses in token handling, trust relationships, or session management to compromise security. Poor token validation, such as missing signature checks or improper storage, allows attackers to replay or steal tokens, impersonating users. Excessive attribute release or misconfigured trust settings can leak sensitive data or enable privilege escalation. Weak trust relationships, like expired certificates or unsecured endpoints, enable spoofing of IdPs or SPs. Relying on a single, compromised IdP creates a high-value target, risking widespread access. Session weaknesses, including long-lived tokens or lack of revocation, can lead to continued unauthorized access after user deprovisioning. Proper security measures, including robust validation and monitoring, are critical to mitigating these vulnerabilities. Recognizing these vulnerabilities helps you implement effective safeguards and reduce federation-related risks. Additionally, implementing encryption protocols can protect token integrity during transmission, further enhancing security. A thorough understanding of trust model configurations is vital to identify potential points of failure and strengthen the overall security posture. Regular security assessments and updates are necessary to adapt to evolving threats in the landscape of identity federation. For example, incorporating continuous monitoring can help detect suspicious activities promptly and prevent breaches.
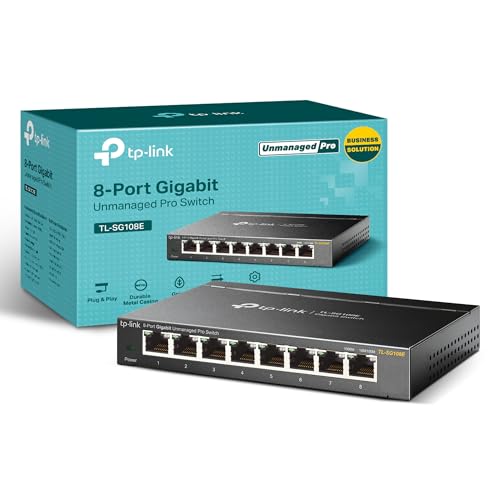
TP-Link 8 Port Gigabit Switch | Easy Smart Managed | Plug & Play | Desktop/Wall-Mount | Sturdy Metal w/ Shielded Ports | Support QoS, Vlan, IGMP and LAG (TL-SG108E)
𝟴 𝗚𝗶𝗴𝗮𝗯𝗶𝘁 𝗘𝘁𝗵𝗲𝗿𝗻𝗲𝘁 𝗣𝗼𝗿𝘁𝘀: expand your network with 8 high-speed ethernet ports
As an affiliate, we earn on qualifying purchases.
Best Practices for Securing Federation Protocols

To strengthen your federation security, you need to enforce strict validation of tokens to prevent impersonation and replay attacks. Using short-lived tokens minimizes the risk if a token is compromised and helps guarantee timely revocation. Additionally, implementing adaptive security measures that respond to emerging threats can further protect your federation environment. Regularly updating your security policies ensures that your protocols stay ahead of potential vulnerabilities. By combining these practices, you create a more resilient federation that maintains trust and integrity across all connected partners. Incorporating strict validation processes ensures that only legitimate tokens are accepted, further enhancing your security posture. Implementing reliable infrastructure supports consistent enforcement of these protocols and reduces potential vulnerabilities. Considering the use of token expiration strategies can also help mitigate risks associated with compromised credentials.
Enforce Strict Validation
Enforcing strict validation of federation tokens is essential to prevent impersonation and token theft. You should verify token signatures using trusted certificates, confirming authenticity. Check the issuer’s identity to confirm the token comes from a trusted IdP, not an attacker. Validate the audience to ensure the token is intended for your service, preventing misuse. Timestamps like expiration and not-before claims must be scrutinized to avoid replay attacks. Additionally, enforce token freshness by rejecting outdated assertions. Use short-lived tokens with refresh controls to limit exposure if a token is compromised. Regularly update and manage cryptographic keys and certificates, and monitor validation logs for suspicious activity. Proper validation procedures are crucial for maintaining secure federation protocols and preventing potential vulnerabilities. Implementing cryptographic key rotation practices further enhances security by reducing the impact of key compromise. Ensuring robust validation checks helps uphold trust in the federation process and safeguard your systems from malicious threats. Incorporating continuous monitoring and alerting can help detect and respond to suspicious validation failures promptly. Moreover, establishing a comprehensive validation policy ensures consistent enforcement of security standards across your federation environment.
Use Short-Lived Tokens
Using short-lived tokens is a key best practice for securing federation protocols because it minimizes the window of opportunity for attackers if a token is compromised. By limiting token lifespan, you reduce the risk of stolen tokens being used maliciously. Short-lived tokens ensure that even if an attacker intercepts or replays a token, its usefulness is limited to a brief period. This approach encourages frequent re-authentication, which helps detect suspicious activity sooner. Additionally, pairing short-lived tokens with refresh tokens allows legitimate users to maintain seamless access without prolonged exposure to potential threats. Proper token expiration management is critical to balancing security and usability, preventing long-term session hijacking while supporting a smooth user experience. Implementing secure token management practices further enhances overall system security by ensuring tokens are generated, stored, and invalidated properly. Incorporating automated monitoring can help detect anomalies in token usage and respond swiftly to potential breaches.
Deployment Patterns and Architectural Considerations

When choosing a federation model, you need to balance scalability, control, and risk, whether you opt for hub-and-spoke, brokered, or direct federation. Selecting the right protocols—like SAML for enterprise environments or OAuth2/OIDC for web and mobile apps—also impacts your architecture’s security and flexibility. Consider how your deployment architecture, whether on-premises, cloud, or hybrid, influences provisioning, trust management, and ongoing maintenance.
Federation Model Choices
Which federation model best fits your organization’s needs depends on your security requirements, scalability goals, and existing infrastructure. Your choice affects trust management, complexity, and potential attack surface.
| Model | Key Characteristics |
|---|---|
| Hub-and-Spoke | Central IdP manages all trust, simplifying setup but creating a single point of failure. |
| Brokered Federation | An intermediary translates protocols, ideal for heterogeneous systems but adds complexity. |
| Direct Federation | One-to-one trust between IdP and SP, offering tighter control but less scalable. |
Consider your growth plans, security posture, and technical capabilities to select the most suitable pattern, balancing control and complexity.
Protocol and Architecture Selection
Selecting the appropriate protocol and architecture for identity federation is essential to guarantee secure, scalable, and manageable integrations across your security domains. You should choose protocols based on your environment and needs. SAML is ideal for enterprise SSO, offering robust assertions and XML-based messaging. OAuth2 and OpenID Connect (OIDC) suit modern web and mobile apps, providing delegated authorization and simplified token exchanges. Architecture patterns like hub-and-spoke centralize trust in a single IdP, streamlining management but increasing risk concentration. Brokered federation introduces an intermediary for heterogeneous setups, adding complexity. Direct federation enables tighter control with one-to-one trust relationships. When deploying, consider hybrid models and secure connectors for cloud integrations. Selecting the right combination guarantees your federation remains secure, adaptable, and easy to maintain.
Monitoring, Metrics, and Ensuring Compliance

Effective monitoring and metrics are essential to maintaining a secure and compliant federated identity environment. You should track key indicators like help-desk ticket volume, password resets, token lifetimes, and active sessions to evaluate session control effectiveness. Monitoring federation metadata—such as certificate expiration and endpoint availability—helps guarantee operational health. Maintaining detailed audit trails of authentication events and attribute releases supports compliance with regulations like GDPR and enables forensic investigations. Regularly evaluating federation security through penetration tests and protocol reviews identifies vulnerabilities before exploitation. Additionally, measuring the time to revoke accounts and tracking failed assertions highlight potential security gaps. By continuously analyzing these metrics, you can promptly detect anomalies, enforce policies, and uphold the integrity and compliance of your federated identity ecosystem.
Practical Strategies for Hardening Federation Security

Securing federated identity environments requires implementing multiple layered measures to prevent unauthorized access and data breaches. First, enforce strict token validation by verifying signatures, issuers, audience, and timestamps. Use short-lived tokens and control refresh tokens to limit exposure. Apply least-privilege attribute release, sharing only essential data with scoped claims to reduce privilege escalation risks. Strengthen IdP protections by enforcing multi-factor authentication, managing certificates proactively, and auditing trust metadata regularly. Secure session handling by enabling token and session revocation, especially during user deprovisioning, and monitor for unusual token activity with real-time alerts. Finally, adopt zero-trust principles, incorporating contextual access controls such as device health, location, and risk scores at SPs. These practices collectively fortify your federation’s security posture against evolving threats.
Frequently Asked Questions
How Do Federated Identity Protocols Handle Attribute Privacy Concerns?
You control attribute privacy in federation protocols by applying least-privilege attribute release, sharing only necessary data with scoped claims. Protocols like SAML, OAuth2, and OpenID Connect support encryption and signing to protect attribute integrity and confidentiality. You should also enforce strict attribute mapping, limit disclosures, and monitor attribute exchange to prevent privilege escalation or data leaks, ensuring user privacy remains intact across federated sessions.
What Are the Risks of Single Points of Failure in Federation Models?
Think of a federated identity system as a tightrope walk—one misstep can cause a fall. You face the risk of a single point of failure when the central IdP goes down, causing all linked services to become inaccessible. If the IdP is compromised, attackers could gain access to multiple service providers. Relying heavily on one IdP makes your entire federation vulnerable to outages and security breaches.
How Can Organizations Detect and Respond to Federation Impersonation Attacks?
You can detect federation impersonation attacks by monitoring for unusual activity, such as unexpected access patterns or logins from unfamiliar locations and devices. Implement real-time anomaly detection, review audit logs regularly, and set up alerts for suspicious behavior. To respond, revoke compromised tokens promptly, enforce multi-factor authentication, and perform thorough investigations to confirm breaches. Strengthen trust relationships and validate tokens securely to prevent future impersonation attempts.
What Role Do Certificate Management Practices Play in Federation Security?
Certificate management practices play a vital role in federation security by ensuring trustworthiness. You should regularly renew, revoke, and verify certificates to prevent impersonation and man-in-the-middle attacks. Properly managing certificate lifecycle, validating signatures, and monitoring expiration dates help keep trust relationships intact. When you enforce strict policies and automate checks, you reduce the risk of compromised certificates, safeguarding your federation from attacks and unauthorized access.
How Is User Session Revocation Managed Across Multiple Federated Service Providers?
You manage user session revocation across multiple federated service providers by implementing centralized token revocation and session management policies. When a user’s access needs to end, you revoke tokens at the identity provider and ensure SPs check token validity regularly. Using short-lived tokens, real-time monitoring, and session revocation protocols helps prevent continued access after deprovisioning, maintaining security across all federated platforms.
Conclusion
As you implement federation solutions, remember that the true challenge lies in staying ahead of evolving threats. With the right strategies, monitoring, and best practices, you can safeguard your identity ecosystem without compromising convenience. But the landscape is constantly shifting—are you prepared to adapt and defend against the next unforeseen vulnerability? Stay vigilant, keep learning, and guarantee your federation remains resilient in the face of emerging risks. The future of secure identity depends on it.









